If an inspector asks who recorded a batch weight at 2:47 PM last Tuesday, can your system answer?
Attributable data integrity cannabis operations depend on one foundational rule: every record must be traceable to the person who created it. The Attributable principle is the first letter in the ALCOA++ data integrity framework, and it is the one that cannabis facilities violate most often without realising it. When three operators share a single login on a desktop terminal during a shift, an inspector reviewing your batch records cannot determine who actually weighed a lot, approved a transfer, or flagged a deviation. That ambiguity alone can trigger a non-compliance finding.
This guide defines what “Attributable” means under international GMP standards, explains why it matters specifically for cannabis manufacturing under Health Canada’s Good Production Practices (GPP), identifies the most common attribution failures, and outlines how individual authentication, granular permissions, and purpose-built temporary labour roles close the gap. This article is part of our comprehensive ALCOA++ Data Integrity for Cannabis Manufacturing guide.
What Does “Attributable” Mean for Cannabis Data Integrity?
The answer comes directly from the regulatory source. PIC/S PI 041-1, the definitive international guidance on data integrity published by the Pharmaceutical Inspection Co-operation Scheme (whose member authorities include Health Canada), defines the Attributable principle as follows: “It should be possible to identify the individual or computerised system that performed a recorded task and when the task was performed. Data must be traceable to the person who generated it.”
In practical terms, this means every entry in your batch records, every weight recorded, every quality inspection completed, and every lot transfer approved must carry two pieces of information: the identity of the person who performed the action, and the timestamp of when they performed it. The principle extends beyond simple record creation. Corrections, deletions, and approvals must also be attributed to a specific individual. If a weight is changed after initial entry, the system must record who made the change, when, and why.
The Attributable principle aligns with requirements across every major regulatory framework that touches cannabis manufacturing. The FDA’s 21 CFR Part 11 mandates that electronic signatures be unique to one individual and never reused or reassigned. The upcoming revision of EU GMP Annex 11, which will explicitly reference ALCOA+ for the first time, underscores the growing regulatory emphasis on data integrity (see our ALCOA++ hub for the full regulatory landscape). Health Canada’s GPP Guide for Cannabis requires that batch records, deviation reports, and complaint files include documentation of who performed each activity.
Because shared accounts are the default in most cannabis production environments, and they make attributable data integrity cannabis compliance structurally impossible.
Here is the typical scenario. A cannabis facility has one or two desktop computers on the production floor, running the seed-to-sale platform. The day shift starts at 6:00 AM. The first operator logs in. Over the next 10 hours, four or five different people use that same session to record weights, complete inspections, and approve transfers. The system stamps every record with the same user ID. When an inspector reviews those records six months later, there is no way to determine which person actually performed each action.
This is not a theoretical risk. Health Canada’s most recent compliance data confirms that documentation deficiencies remain a persistent finding in cannabis inspections, and attribution gaps fall squarely within that category: if the system cannot prove who created a record, the record’s integrity is in question (see our complete ALCOA++ guide for the latest enforcement numbers).
The problem is compounded by the physical reality of cannabis production. Operators move between rooms, handle plant material with gloved hands, and work in environments where stopping to log in and out of a desktop terminal is impractical. The result is that shared sessions persist for entire shifts, and the Attributable principle is violated on every single record created during that time. This shared-login pattern also enables delayed data entry, compounding the violation with a Contemporaneous principle failure.
What Are the Most Common Attribution Failures in Cannabis Operations?
Attribution failures fall into four categories, each progressively harder to detect during an inspection.
The most obvious failure. Multiple operators use one account, and the system has no way to distinguish between them. This violates the core Attributable requirement. Some facilities create “generic” accounts like “DayShift1” or “ProductionFloor” to simplify access, which makes the problem even worse by design.
2. Missing Signature Fields
Batch records that capture the action (weight recorded, inspection completed) but not who performed it. Paper forms may have a signature line, but it is frequently left blank or initialled illegibly. Digital systems without mandatory “performed by” fields create the same gap.
3. No Separation of Duties
When the same person who weighs a lot also approves the weight, there is no independent verification. GMP environments require distinct “performed by” and “verified by” roles. Without role-based permissions that enforce this separation, a single operator can record and approve their own work, undermining the integrity of the entire batch record.
Even when a facility requires individual logins, the benefit disappears if a session remains active after the authenticated operator walks away. The next person who picks up the device inherits the previous user’s identity. Without automatic session expiry, shared devices on the production floor become shared accounts in practice.
| Failure Type | How It Happens | Inspector Impact |
|---|---|---|
| Shared user accounts | Multiple operators use one login on a desktop terminal | Cannot determine who recorded any individual action |
| Missing signature fields | Forms lack mandatory “performed by” or “verified by” fields | Batch record shows what happened but not who did it |
| No separation of duties | Same person records and approves their own work | No independent verification; self-approval compromises integrity |
| No inactivity timeout | Authenticated session persists after operator walks away | Records attributed to wrong person; shared device becomes shared account |
GrowerIQ Mobile Scanner
See how it supports attributable record-keeping on the facility floor
Individual authentication and role-based permissions tie every action to a named user.
Explore the Scanner →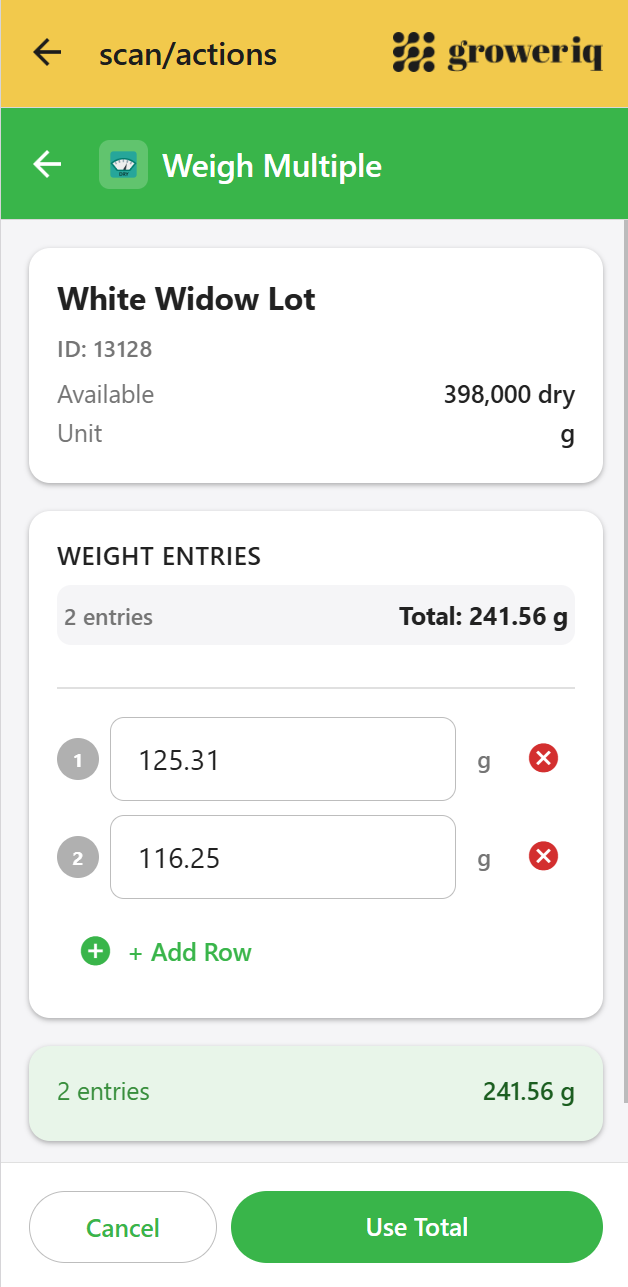
How Do You Support Attributable Data Integrity in Cannabis Manufacturing?
The solution requires four layers working together: individual authentication, granular role-based permissions, purpose-built temporary labour roles, and automatic session management on shared devices.
Individual Authentication on Every Device
The foundation is simple: every person who touches a record must log in with their own credentials. This means eliminating shared accounts entirely. OAuth 2.0-compliant identity providers make individual authentication practical even in high-turnover production environments. Each operator gets their own login. Every action they take is stamped with their unique user identity, drawn from the authentication token (JWT) that their session carries.
For facilities using mobile scanners on the production floor, individual authentication becomes even more practical than desktop logins. An operator picks up a shared handheld device, logs in with their own credentials, completes their tasks, and the device locks after a period of inactivity (typically five minutes). The next operator authenticates fresh. Every record carries the correct identity.
Granular Role-Based Permissions
Authentication tells you who is logged in. Permissions tell you what they are allowed to do. A robust attributable data integrity cannabis system needs permissions granular enough to enforce separation of duties at the action level.
Consider a practical example. A production operator should be able to record a weight, but they should not be able to approve a lot for release. A QA reviewer should be able to approve a lot, but they should not be able to modify the original weight. A shift supervisor might need both capabilities. These distinctions require permissions mapped to specific actions, not broad “admin” or “user” roles.
GrowerIQ’s mobile scanner supports permissions mapped to individual actions (weighing, inspecting, transferring, approving) rather than broad roles, controlling access at the action level. Each role in the system is configured with a specific set of permissions, and the scanner enforces these permissions in real time. If a permission check fails to load, the scanner defaults to denying access (fail-closed design), ensuring that an operator never accidentally gains access to actions outside their role.
Temporary Labour Roles: Micro-Permissions for Casual Workers
Cannabis facilities frequently hire temporary workers for harvest, trimming, and packaging. These workers need to record data (contemporaneous capture is critical), but they should not have access to sensitive operations like lot approval, transfers, or inventory adjustments. The challenge is giving casual workers enough access for data entry while protecting the integrity of higher-level operations.
Custom temporary labour roles solve this. A facility can create a role with micro-permissions that allow a temporary worker to record weights, complete visual inspections, and scan barcodes, but restrict them from approving batches, modifying existing records, or accessing financial data. The temporary worker logs in with their own individual account, every action they take is attributed to them personally, and the facility maintains full control over what they can and cannot do. This opens up contemporaneous data capture to the entire workforce without compromising data protection.
Shared handheld devices on the production floor require automatic session expiry. A five-minute inactivity timeout ensures that if an operator sets down a device and walks away, the next person who picks it up must authenticate before interacting with the system. This closes the gap between individual authentication and real-world floor behaviour, where devices change hands frequently.
Attribution Fields on Every Activity
The technical foundation for all of this is structured attribution data on every record. Each activity captured in the system should include distinct fields for “weighed by,” “checked by,” and “approved by,” each populated from the authenticated user’s identity. These fields are not optional text inputs that operators might skip. They are system-generated from the authentication token, ensuring that attribution is automatic, consistent, and tamper-resistant.
Paper vs Digital: How Does Each Approach Handle Attribution?
The difference between paper-based and digital attribution is structural, not procedural. Paper depends on human compliance (signing the form, initialling the entry). Digital systems enforce attribution automatically through authentication.
| Attribution Requirement | Paper-Based | Digital (Mobile with Individual Auth) |
|---|---|---|
| Individual identity on each record | Partial. Relies on handwritten signatures that can be forged, illegible, or skipped. | Supported. User identity from authentication token on every action. |
| Separation of duties | Partial. Relies on operators following procedure; no enforcement mechanism. | Supported. Role-based permissions enforced at the action level. |
| “Performed by” / “Verified by” fields | Partial. Fields exist on paper forms but are frequently left blank. | Supported. System-generated from JWT; cannot be skipped. |
| Temporary worker access control | Not supported. Paper forms have no permission layer; any worker can fill in any field. | Supported. Custom roles with micro-permissions restrict access by action type. |
| Session management on shared devices | Not applicable. Paper has no session concept. | Supported. Automatic inactivity timeout forces re-authentication. |
| Tamper-resistant attribution | Not supported. Signatures can be added after the fact; no audit trail of changes. | Supported. Attribution data is system-generated and immutable. |
The critical distinction is enforcement. Paper-based systems rely on every operator, every time, following the correct procedure. Digital systems with individual authentication enforce attribution structurally. The operator cannot submit a record without being authenticated, and the system cannot generate a record without embedding the operator’s identity. The human compliance requirement is removed from the equation.
Key Takeaways
- Attributable means traceable to one person: Every record must identify who created it and when, per PIC/S PI 041-1 and aligned with Health Canada GPP, FDA 21 CFR Part 11, and EU GMP Annex 11 requirements.
- Shared logins are the #1 violation: Desktop terminals with shared accounts make it impossible to determine who performed a specific action, undermining the entire batch record’s integrity.
- Four layers solve the problem: Individual authentication, granular role-based permissions mapped to specific actions, custom temporary labour roles, and automatic inactivity timeouts work together to support attributable data integrity.
- Temporary workers need access, not free rein: Micro-permissions let casual labourers record data contemporaneously while restricting access to sensitive operations.
- Software is the foundation, not the finish line: Facility-level validation (IQ/OQ/PQ) by your quality team completes the attribution picture.
Frequently Asked Questions
What does attributable data integrity mean in cannabis manufacturing?
Attributable data integrity in cannabis means every batch record, weight entry, inspection result, and approval is traceable to the specific individual who performed it. The PIC/S PI 041-1 guidance defines it as the ability to “identify the individual or computerised system that performed a recorded task and when the task was performed.” In practice, this requires individual user accounts (no shared logins), role-based permissions, and system-generated identity fields on every record.
Health Canada’s Good Production Practices require that batch records and operational documentation demonstrate compliance with Cannabis Regulations Part 5. If an inspector cannot determine who created a specific record because multiple operators shared the same account, that record’s integrity is compromised. While Health Canada does not name “shared logins” explicitly, the requirement for attributable documentation means shared accounts create a direct compliance risk.
How do you handle attribution for temporary or seasonal workers?
Create individual accounts for every temporary worker and assign them to a custom role with micro-permissions. This role should allow the actions temporary workers need to perform (recording weights, completing inspections, scanning barcodes) while restricting access to sensitive operations (lot approval, record modification, inventory adjustments). Each temporary worker’s actions are attributed to their personal account, maintaining full traceability without compromising data protection.
What is the connection between attributable data integrity and 21 CFR Part 11?
FDA 21 CFR Part 11 requires that electronic signatures be unique to one individual, never reused or reassigned, and employ at least two distinct identification components. These requirements are the regulatory implementation of the Attributable principle for electronic records. Meeting ALCOA++ attribution objectives through individual authentication and role-based permissions supports Part 11 alignment. See our CFR Part 11 digital signatures feature page for more detail.
Validation Disclaimer: ALCOA++ data integrity is achieved through validated processes at your facility. GrowerIQ provides the software foundation that supports each ALCOA++ principle; your quality team completes the validation documentation (IQ/OQ/PQ) as part of your facility’s quality management system.
See How Individual Authentication Supports Attributable Data Integrity
See how role-based permissions and individual authentication on GrowerIQ’s mobile scanner support attributable records.
EXPLORE SCANNER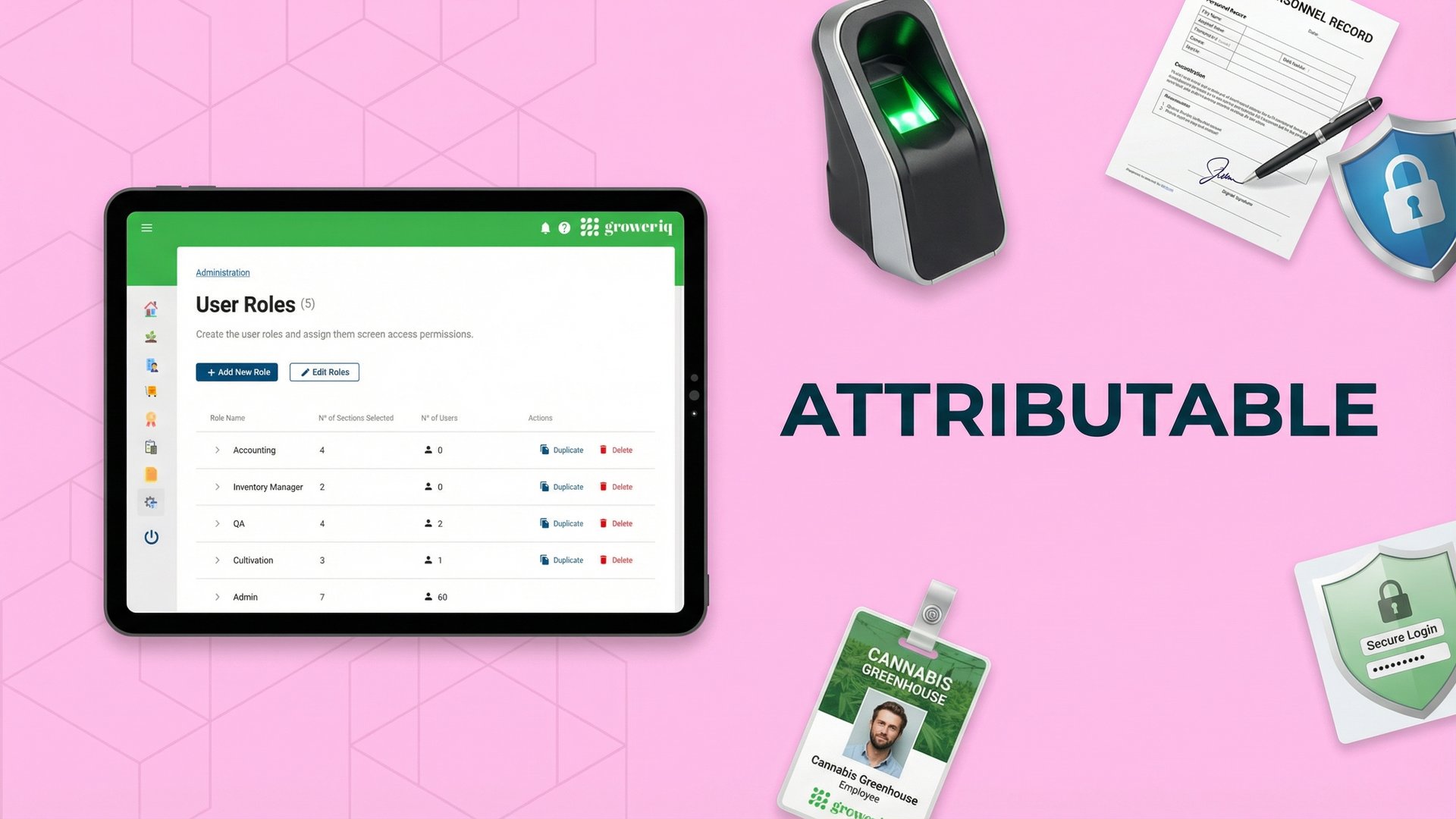
Last updated: March 2026
About GrowerIQ
GrowerIQ is changing the way producers use software - transforming a regulatory requirement into a robust platform to learn, analyze, and improve performance.
To find out more about GrowerIQ and how we can help, fill out the form to the right, start a chat, or contact us.